Detect SolarWinds SUNBURST Malware and Protect your Network with BLUE LANCE’s LT Auditor+
Overview
On 12/13/2020, FireEye released a malware report on a new malware variant called “Sunburst Backdoor” that precipitated the Department of Homeland Security’s CISA (Cybersecurity and Infrastructure Agency) to issue an emergency directive.
The Sunburst malware ‘trojanized’ […]
Protecting and Monitoring Home Workers Workstations’ increases Security & Compliance
You planned for ongoing modernization of your corporate network and infrastructure but who knew that the PANDEMIC was coming to eat your lunch … and dinner?
What to do when you are not able to give […]
YOUR INSIDER THREAT JUST MOVED OUTSIDE YOUR FIREWALL !
YOUR INSIDER THREAT JUST MOVED OUTSIDE YOUR FIREWALL !
You must increase protection of your Home Workers. BLUE LANCE HELPS
Auditing & Compliance must now expand to include remote workstations!
BLUE LANCE is taking immediate steps to assist businesses in […]
Blue Lance Is Giving Schools and Colleges Cybersecurity Tools For Free
_______________________________________________________________________________________________________________________________
“COVID-19 should not be allowed to disrupt the education of our kids. They should be able to continue learning safely from home during this time”
Umesh Verma, CEO, BLUE LANCE
_______________________________________________________________________________________________________________________________
As schools shut down in an effort […]
Ransomware research shows attacks are expensive and pervasive.
Ransomware research shows that the costs of ransomware attacks and recovery continue to be very expensive and pervasive. A recent report by the security team at KPN, a Dutch telecommunications provider indicates their research over […]
Cybersecurity tools are complicated and expensive! What does a business leader do?
The cost of breach events is estimated at nearly $900,000 for even small and mid-sized businesses. It is a huge expense and it continues to climb. A ransomware attack can be a truly existential event […]
Fostering Cybersecurity Education and Discussion with C-Level Banking Executives
I had a conversation with a C-level banker last week who asked me what my mission, our company’s mission is. Here is how I replied:
Fostering education and discussion about affordable and effective cybersecurity and compliance […]
Surviving a Breach
Banking Viability in a threatening world of Cyber-Insecurity
You will be breached, there is no doubt. What you do about it is critical.
Cybersecurity is creating a lot of noise and many claims are being made about […]
Banking Viability in a threatening world of Cyber-Insecurity:
How can you cost effectively secure your Bank’s business information, protect your assets and reputation and ensure your long-term viability?
A mature Cybersecurity posture and business recovery preparations are necessary to survive in today’s threatening environment […]
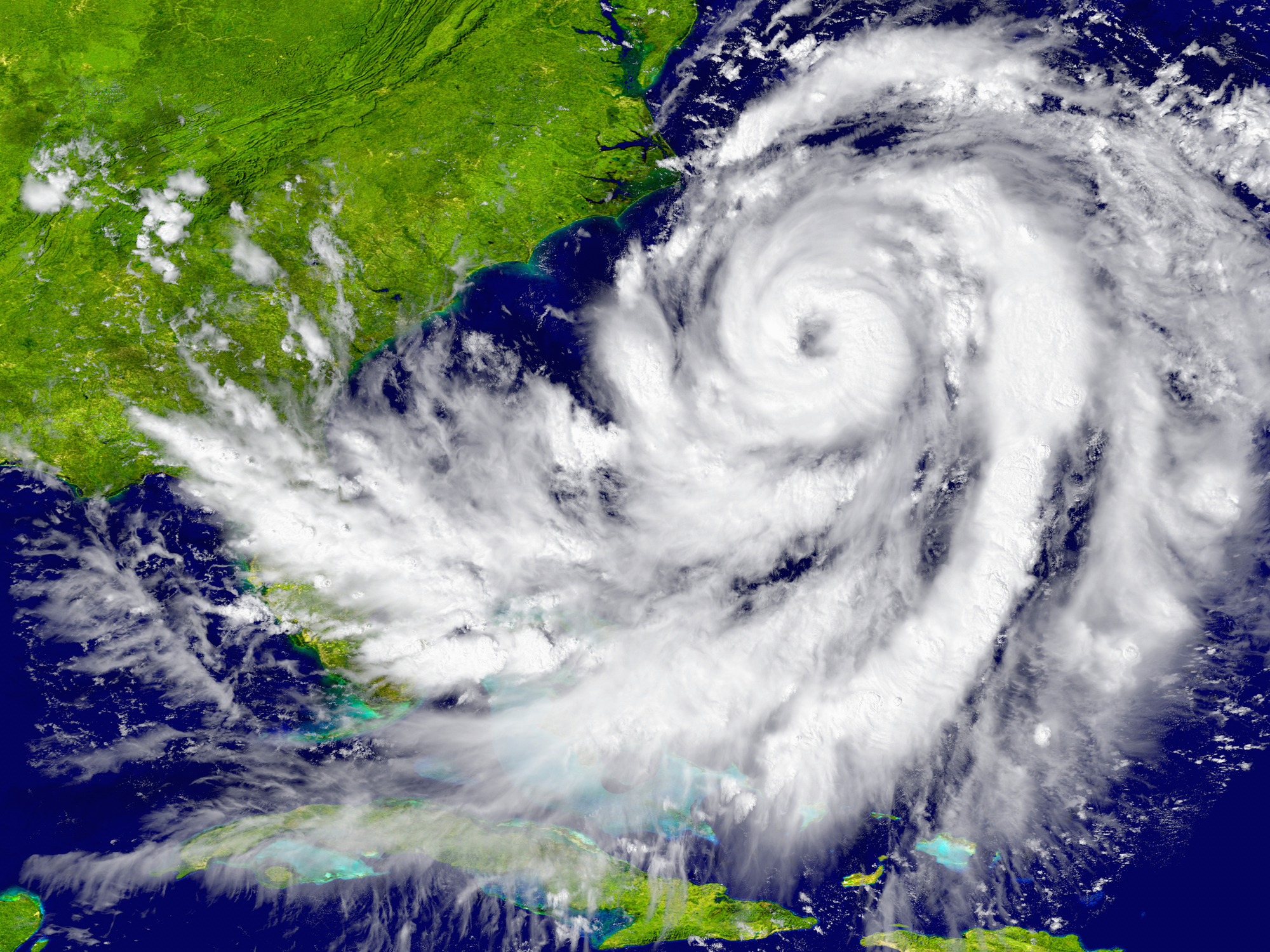
Harvey, Irma, and You: Protecting Your Business from Cyber Criminals after a Natural Disaster
It’s a sad reality: When a natural disaster hits, it brings on more than a storm surge. Surges in cybercrime rise as well.
This year has been particularly devastating for natural disasters. Our very own Houston […]




Get Social