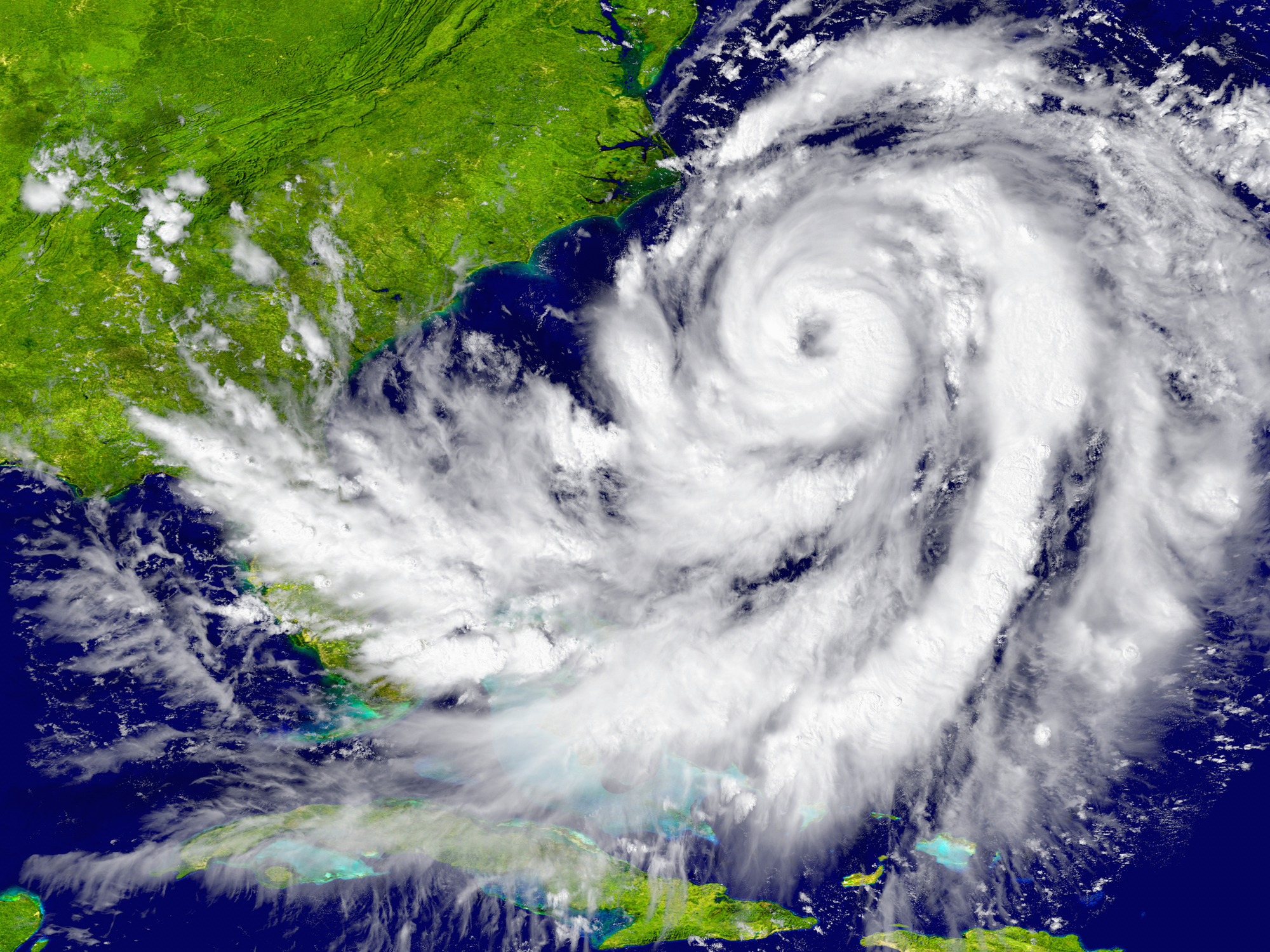
Harvey, Irma, and You: Protecting Your Business from Cyber Criminals after a Natural Disaster
It’s a sad reality: When a natural disaster hits, it brings on more than a storm surge. Surges in cybercrime rise as well.
This year has been particularly devastating for natural disasters. Our very own Houston was hit hard by Hurricane Harvey. Florida was pummeled, causing record level flooding when Hurricane Irma made landfall. Mexico has […]