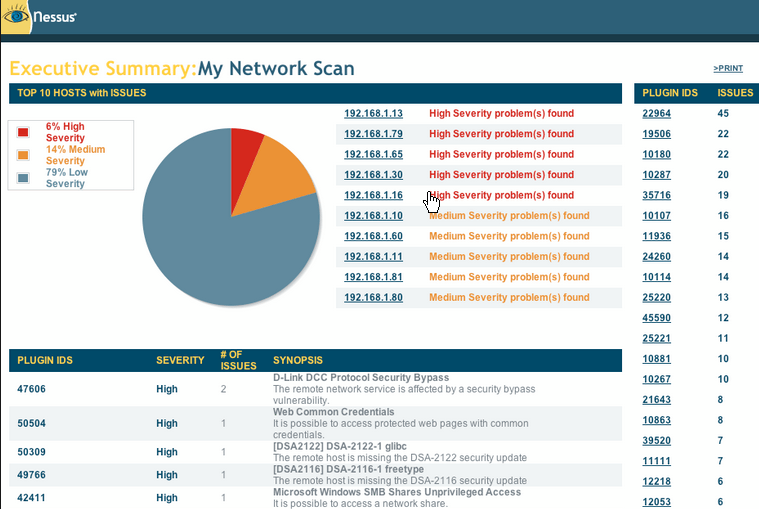
Vulnerability Scanning is a service where a suite of testing tools are used to scan your network looking for vulnerabilities. The vulnerabilities discovered will be ranked by level of severity for each IP address with recommendations for remediation. The goal of the vulnerability scanning service is to provide customers with an ongoing scanning program that will help them stay ahead of attackers. Multiple tools are leveraged for a much better view of the security posture. These tools include commercial, open source and other tools as they become available.

OUR PROCESS
- Work with customers to collect contact lists (name, phone, pager, cell) of all technical team members that will interface with our consultants.
- Customer will assign a primary contact to the project described the applicable Statement of Work SOW prior to delivery of any services.
- Will host periodic status meetings to discuss progress and issues with customer’s primary contact.
- Will collect customer’s current Disaster Recovery or Business Continuity plans, security policy, procedure or process document relevant to this project upon commencement.
DELIVERABLES
- Vulnerability Scan Report and recommendations for remediation.