Microsoft uses two types of protocols for authentication namely:
- Kerberos authentication (default)
- NTLM authentication
A brief explanation of these protocols will provide more clarity on understanding the LT Auditor+ login activity associated with tracking account lockouts.

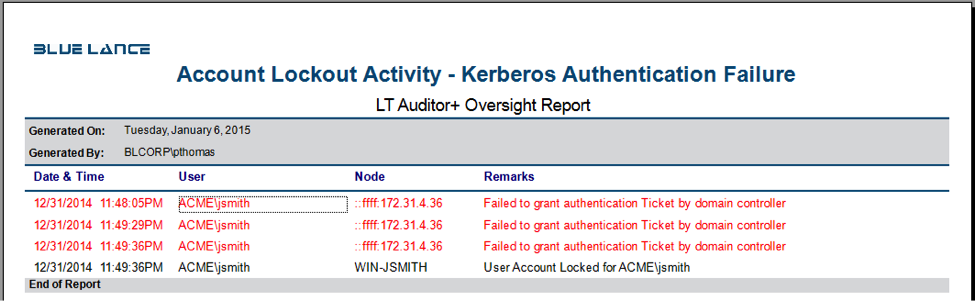
Kerberos authentication
The report show the how user jsmith’s account was locked after multiple login attempts from the workstation node 172.31.4.36. The login failures reported were caused by pre-authentication Kerberos login failure identifying the IP address of the node which caused the failure.
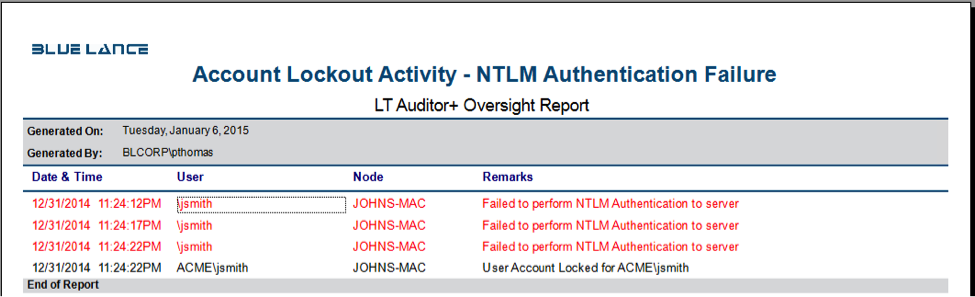
NTLM Authentication
The report show the how user jsmith’s account was locked after multiple login attempts from the workstation ‘JOHNS-MAC’. The login failures reported were caused by NTLM authentication failure identifying the workstation node which caused the failure.
Benefits of tracking and monitoring account lockout activity with LT Auditor+
- Identify account lockouts in real time to ensure that a dictionary attack is not being attempted on the network. Email alerts can be triggered only when specified powerful accounts are locked out.
- Troubleshoot account lockouts to find causes of account lockouts and prevent loss of productivity, end user frustration and improve incident response with high quality reports.
- Meet compliance requirements from SOX, PCI-DSS, HIPAA, FFIEC and NIST by comprehensively tracking and monitoring account lockout activity.
- Monitor access by privileged user accounts for compliance and accountability and get real time notification if any of these user accounts get locked out.
About LT Auditor+
LT Auditor+ is a suite of applications that provide real-time monitoring and auditing of Windows Active Directory & Windows Servers changes. The application audits-tracks-reports on Windows Active Directory, Windows Workstations Logon / Logoff, Windows File Servers & Member Servers to help meet security, audit and compliance demands or requirements. Track authorized / unauthorized access of users Logon / Logoff, GPO, Groups, Computer, OU, DNS server changes with over 300 detailed event specific reports and real-time email alerts. Reports generation can automated and scheduled and can be exported to multiple formats like PDF, EXCEL, HTML and CSV that further assist with a forensic investigation.